UIAO Modernization Atlas
Identity-Driven Infrastructure for FedRAMP Moderate Environments
1 The Problem
Federal agencies operating FedRAMP Moderate environments contend with fragmented identity systems, manual compliance evidence collection, and no cross-service telemetry. Legacy ICAM, network, and compliance tools operate as independent silos — each authoritative within its domain, none aware of the others. When an identity event occurs — a joiner, mover, or leaver — there is no deterministic way to trace its effects across all dependent systems in real time.
The consequence is twofold: security gaps widen between identity events and their downstream enforcement, and compliance evidence remains point-in-time rather than continuous.
2 The Solution
The Unified Identity-Addressing-Overlay Architecture (UIAO) is a drop-in overlay that restores cross-service telemetry and identity correlation in FedRAMP Moderate environments where native platforms cannot. UIAO sits atop existing vendor stacks — Azure Active Directory, Cisco ISE, Palo Alto Networks, Infoblox, Microsoft Sentinel — and provides deterministic identity-to-addressing correlation, real-time drift detection, and OSCAL-native compliance automation. No rip-and-replace of existing infrastructure is required. Existing authorizations, integrations, and tooling are preserved; UIAO adds the correlation layer they lack.
3 Key Outcomes
| Outcome | Description |
|---|---|
| Leaver Killswitch: <120 seconds | An identity termination event propagates to network enforcement (ISE policy, DNS/DHCP revocation, SD-WAN segmentation) within two minutes, deterministically. |
| Continuous Compliance Evidence | Control satisfaction is captured at event time, not assembled at audit time. OSCAL artifacts reflect current posture rather than a snapshot. |
| Cross-Service Telemetry Correlation | Identity events, network state changes, and security signals are correlated in a single data model. No manual log correlation required. |
| OSCAL-Native SSP and POA&M | System Security Plans and Plans of Action and Milestones are generated directly from the UIAO canon. FedRAMP 20x machine-readable submission is supported natively. |
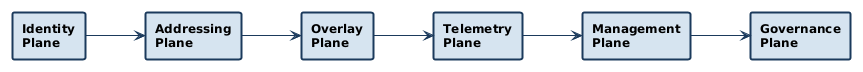
4 Six Control Planes
UIAO is organized as six discrete control planes. Each plane owns a specific operational domain; together they form a closed-loop system where identity state drives all downstream enforcement and compliance reporting.
| Plane | Domain | Representative Components |
|---|---|---|
| Identity | Authentication, authorization, joiner/mover/leaver lifecycle | Azure Active Directory, Cisco ISE |
| Addressing | IP address, DNS, and DHCP lifecycle correlated to identity | Infoblox DDI/IPAM |
| Overlay | Network segmentation, path enforcement, micro-perimeter | Palo Alto NGFW, Cisco SD-WAN |
| Telemetry | Event correlation, anomaly detection, continuous monitoring | Microsoft Sentinel, Splunk |
| Management | Orchestration, policy distribution, drift remediation | Automation layer, API fabric |
| Governance | Compliance artifact generation, provenance tracking, audit evidence | OSCAL SSP, POA&M, Component Definitions |
5 Who This Is For
This Atlas is written for federal technical and compliance practitioners who own or assess FedRAMP Moderate system authorizations:
- Federal CISOs and CIOs evaluating identity-driven zero trust architecture
- FedRAMP Assessors (3PAOs) reviewing continuous monitoring posture and control implementation
- Compliance Officers responsible for SSP currency, POA&M management, and audit evidence
- IT Modernization Program Managers replacing legacy ICAM, DDI, and network segmentation infrastructure
- Security Architects designing zero trust network access in hybrid cloud environments